Introduction
If you have a SPA built with any JavaScript framework and it has an attachment feature, you must hit the part where you need to allow the user to download an attachment and the App is authenticating users using Tokens.
The problem
With normal forms authentication based on cookies the browser will simply send the authentication cookie with each request to your web server without you doing anything. If you have a link that will allow the user to download a file from your server, the browse will automatically send the authentication cookie when the user clicks the link. This makes it so easy for you. But if you are using token based authentication, it is your responsibility to send a token for each request sent to the server via Ajax by using the Authorization header.
Unfortunately, you cannot control the headers sent to the server if the user is opening a link in a new browser window and the user will end up with unauthorized request.
The solution
Download the file using Ajax Request
In this solution, you have to request the endpoint that downloads the file using Ajax Request which will include the authorization header and then get all the file content in a variable and push the content to the user. This works fine if the file size is very small. But imagine the case when you are downloading a 500MB file. This is not going to work since the file is stored in a JavaScript variable before the download takes place.
Make the API that download the attachment anonymous
If the endpoint that downloads the file doesn’t require authentication then we are good. But now the file will be available for every one to download. So, we have to find a way to secure the file even when the endpoint is anonymous.
If you have some experience with Azure Storage, you may have heard of Azure Storage Shared Access Signature. The idea is simple. When the user requests a file, generate a token, save it to a temporary storage and append it to the URL of the download file endpoint. When the user clicks the link, the endpoint will be called and the token will be validated against the temporary storage and if it matches then send the file contents. This way we will be sure that the link was generated by the application to that user. Still, if the link was shared to another user, he will be able to download the file. But this is another issue that we can worry about later.
Implementation
We will create a new asp.net core site with an endpoint to download files but I will not create a SPA in this article. That will be left for the reader. I will test the idea though using Postman.
Open Visual Studio, Create a new project of type “Asp.NET Core Web Application” then Choose “API” in the next dialog. You can still choose “Web Application (Model-View-Controller)”. I will leave authentication to the default “No Authentication”.
Right Click on the Controllers folder and choose “New Controller”, choose “API Controlller – Empty” and name it AttachmentsController. You should end up with the following
[Produces("application/json")]
[Route("api/Attachments")]
//[Authorize]
public class AttachmentsController : Controller
{
}
Notice that I have commented the [Authorize] attribute since I didn’t setup authentication in this demo. In real life scenario, you will setup authentication and authorization using Token based Authentication.
Create a folder named Services and then create a new interface called ISecureUrlGenerator. The content should look like the following:
public interface ISecureUrlGenerator
{
string GenerateSecureAttachmentUrl(string id, string url);
bool ValidateUrl(string url, string id);
bool ValidateToken(string id, string token);
}
Now, add class to implement the previous interface
using Microsoft.Extensions.Caching.Memory;
using System;
using System.Collections.Generic;
namespace SecureAttachmentsDownload.Services
{
public class SecureUrlGenerator : ISecureUrlGenerator
{
private readonly IMemoryCache memoryCache;
public SecureUrlGenerator(IMemoryCache memoryCache)
{
this.memoryCache = memoryCache ?? throw new ArgumentNullException(nameof(memoryCache));
}
public string GenerateSecureAttachmentUrl(string id, string url)
{
var token = Guid.NewGuid().ToString().ToLower();
StoreToken(id, token);
var separator = url.Contains("?") ? "&" : "?";
return $"{url}{separator}token={token}";
}
public bool ValidateToken(string id, string token)
{
var tokens = memoryCache.Get(id);
if (tokens != null && tokens.Contains(token))
return true;
return false;
}
public bool ValidateUrl(string url, string id)
{
var uri = new Uri(url);
var queryStringParams = uri.Query.Split("&");
foreach (var param in queryStringParams)
{
var values = param.Split("=");
if (values[0].ToLower() == "token")
{
return ValidateToken(id, values[1]);
}
}
return false;
}
private bool IsTokenValid(string id, string token)
{
var tokens = memoryCache.Get(id);
if (tokens != null && tokens.Contains(token))
return true;
return false;
}
private void StoreToken(string id, string token)
{
var tokens = memoryCache.Get(id);
if (tokens == null)
tokens = new List();
tokens.Add(token);
memoryCache.Set(id, tokens);
}
}
}
In this implementation, I am storing the tokens in asp.net core memory cache. To enable this feature, you have to add the caching service in Starup.cs file
public void ConfigureServices(IServiceCollection services)
{
services.AddMemoryCache();
services.AddMvc();
}
You can replace the memory cache with a database if you want the tokens to be permanent and in this case you have to add an expiration date.
Before we utilize the secure URL genrator, we need a class to hold the attachments metadata since the user will request the list of attachments first and then download it.
Create a folder called Models and put the following class in it.
namespace SecureAttachmentsDownload.Models
{
public class AttachmentMetadata
{
public int Id { get; set; }
public string DownloadUrl { get; set; }
public string Name { get; set; }
public int FileSize { get; set; }
}
}
Now, lets get to the part where we utilise our secure URL generator.
The flow will be as below:
- The user requests endpoint to return a list of attachments to be displayed to the user. Here, the DownloadUrl will have the token already. This will be secured by tokens
- The SPA will display this list to the user as links or buttons that the user can click to download the file. The href for the anchor tag will be the DownloadURl property
- The user will click the link to download the attachment
- The AttachmentController will be called and the endpoint will validate the token and return the file or else a 401
Open the AttachmentsController file and add the following 2 action methods
using System.Collections.Generic;
using System.IO;
using System.Linq;
using Microsoft.AspNetCore.Authorization;
using Microsoft.AspNetCore.Hosting;
using Microsoft.AspNetCore.Mvc;
using SecureAttachmentsDownload.Models;
using SecureAttachmentsDownload.Services;
namespace SecureAttachmentsDownload.Controllers
{
[Produces("application/json")]
[Route("api/Attachments")]
//[Authorize]
public class AttachmentsController : Controller
{
private readonly ISecureUrlGenerator _secureUrlGenerator;
private readonly IHostingEnvironment _hostingEnvironment;
private readonly List Attachments = new List()
{
new AttachmentMetadata
{
Id = 1,
Name = "bitcoin.pdf",
ContentType = "application/pdf",
FileSize = 1024
},
new AttachmentMetadata
{
Id = 2,
Name = "report 1.pdf",
FileSize = 3024
},
new AttachmentMetadata
{
Id = 3,
Name = "report 2.pdf",
FileSize = 2024
}
};
public AttachmentsController(ISecureUrlGenerator secureUrlGenerator, IHostingEnvironment hostingEnvironment)
{
_secureUrlGenerator = secureUrlGenerator;
_hostingEnvironment = hostingEnvironment;
}
[HttpGet]
[Route("")]
public IActionResult Get()
{
foreach (var attachment in Attachments)
{
var url = Url.Action(nameof(AttachmentsController.Get), "Attachments", new { attachment.Id }, Url.ActionContext.HttpContext.Request.Scheme);
attachment.DownloadUrl = _secureUrlGenerator.GenerateSecureAttachmentUrl(attachment.Id.ToString(), url);
}
return Ok(Attachments);
}
[HttpGet]
[Route("{id}")]
[AllowAnonymous]
public IActionResult Get(int id, string token)
{
if (!_secureUrlGenerator.ValidateToken(id.ToString(), token))
return Forbid();
var attachment = Attachments.FirstOrDefault(a => a.Id == id);
if (attachment == null)
return NotFound();
var stream = new FileStream($"{_hostingEnvironment.WebRootPath}\\Files\\{attachment.Name}", FileMode.Open);
return File(stream, attachment.ContentType);
}
}
}
Now run the application and open the URL /api/Attachments. You will get the following excepttion:
InvalidOperationException: Unable to resolve service for type ‘SecureAttachmentsDownload.Services.ISecureUrlGenerator’ while attempting to activate ‘SecureAttachmentsDownload.Controllers.AttachmentsController’.
To fix it, open the startup.cs file and add the following line to the ConfigureServices method
public void ConfigureServices(IServiceCollection services)
{
services.AddMemoryCache();
services.AddScoped ();
services.AddMvc();
}
Now open the URL api/attachments again and you should see the following JSON response
[
{
"id": 1,
"downloadUrl": "http://localhost:53098/api/Attachments/1?token=b78763c2-0109-4c12-b771-5f5cc5d19017",
"name": "bitcoin.pdf",
"fileSize": 1024,
"contentType": "application/pdf"
},
{
"id": 2,
"downloadUrl": "http://localhost:53098/api/Attachments/2?token=12497a4a-8f08-44ba-b9f6-914c4b484cc5",
"name": "report 1.pdf",
"fileSize": 3024,
"contentType": null
},
{
"id": 3,
"downloadUrl": "http://localhost:53098/api/Attachments/3?token=8647bb52-e47f-4580-8149-0b1d238ab0e2",
"name": "report 2.pdf",
"fileSize": 2024,
"contentType": null
}
]
As you can see, the downloadUrl property has the absolute URL for the file and the `token` query string parameter is appended. If you open the first link in a new browser window, the Action Get(id) will be called and the token will be bound to the parameter token.
In my implementation, I have put some files in a folder called Files under the wwwroot folder. But in actual projects, you may retrieve the files from a Database, FTP or any Document Management System.
If you want to make sure that it is really working, just try to change any character in the token query string and you should get a forbid response from the server. In this example you will get an exception: InvalidOperationException: No authenticationScheme was specified, and there was no DefaultForbidScheme found.
This is because I didn’t configure the authentication middleware.
You can find the source code for this article on GitHub.
This implementation has as flaw. The list of attachments are returned with the download URL and the tokens are saved in memory. If the user didn’t click the link but after sometime, the tokens may have been already expired. So, either you save the tokens in a DB or you before clicking the link, fire an Ajax request to an endpoint that gets the metadata for a single attachment. This way, the downloadUrl will be always fresh and working.
If you have any questions or suggestions, please leave a comment below.

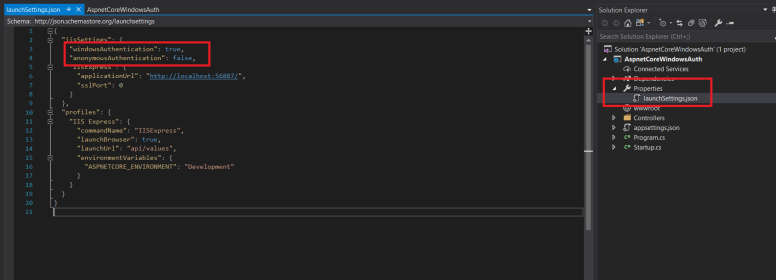 You can also modify the URL and SSL settings.
You can also modify the URL and SSL settings.